--- Corporate ---
Policies and Guidelines
Know Your Customer Policy
-
Know Your Customer is the process of verifying the identity of customer. The objective of KYC guidelines is to prevent banks from being used, by criminal elements for money laundering activities. It also enables banks to understand its customers and their financial dealings to serve them better and manage its risks prudently.
-- Resident Indian citizens
-- Family Trusts
-- Hindu Undivided Family (HUF)
-- Clubs, societies, and associations
-- Sole proprietorship, group companies, and partnership firms -
Importance of KYC
KYC is the means of identifying and verifying the identity of the customer through independent and reliance source of documents, data or information. For the purpose of verifying the identity of:
Individual customers, bank will obtain the customer's identity information, address and recent photograph. Similar information will also have to be provided for joint holders and mandate holders.
Non-lndividual customers banks will obtain identification data to verify the legal status of the entity, operating address, the authorized signatories and beneficial owners. Information is also required on the nature of employment/business that the customer does or expects to undertake and the purpose of opening of the account with the bank
Information is also required on the nature of employment/business that the customer does or expects to undertake and the purpose of opening of the account with the bank. -
Purpose
The KYC guidelines have been put in place by the Reserve Bank of India in the context of the recommendations made by the Financial Action Task Force (FATE) on Anti Money Laundering (AM ) standards and on Combating Financing of Terrorism (CFT). The Prevention of Money Laundering Act requires banks, financial institutions and intermediaries to ensure that they follow certain minimum standard of KYC and AML
-
Periodicity of KYC refresh
KYC is to be provided at the time of opening a new account as well as refresh. It may be necessary to obtain additional information from existing customers based on the conduct of the account, where there are changes to the account or at fixed periodic refresh cycles based on the risk categorization of the customer. Similarly, an existing customer will be required to provide fresh KYC for new account opening to adhere to the latest applicable KYC standards.
-
Contact Person in the bank
As a customer of the bank, you will need to liaise with your Relationship Manager or the bank staff that initiated your account opening.
Failure to provide KYC
Banks are entitled to refuse to open an account or discontinue an existing relationship if there is failure to meet the minimum KYC requirements. However, there is flexibility provided to certain categories of customer who are unable to provide the necessary document at the time of account opening.
ANTI-MONEY LAUNDERING POLICY
-
AML Policy Objectives
Within the overall Group AML Policy framework, the key AML objectives of the Bank are:
--> To prevent the Bank's business channels/products/services from being used as a channel for ML.
--> To establish a framework for adopting appropriate AML procedures and controls in the operations/business processes of the Bank.
--> To ensure compliance with the laws and regulations in force from time to time.
--> To protect the Bank's reputation.
--> To assist law enforcement agencies in their effort to investigate and track money launderers.
--> To lay down AM compliance norms for the employees of the Bank. -
Definition of Money Laundering
ML is the process by which criminals attempt to disguise the true origin of the proceeds of their criminal activities by the use of the financial system so that after a series of transactions, the money, its ownership and the income earned from it appear to be legitimate. According to FATE ML is the processing of criminal proceeds in order to disguise their illegal origin.
This process is often achieved by converting the original illegally obtained proceeds from their original form, usually cash, into other forms such as deposits or securities and by transferring them from one financial institution to another using the account of apparently different persons or businesses.
Section 3 of PMI_A, describes the offence of ML. Section 3 reads as under:
"Whosoever directly or indirectly attempts to indulge or knowingly assists or knowingly is a party or is actually involved in any process or activity connected with the proceeds of crime and projecting it as untainted property shall be guilty of offence of money-laundering." -
Money Laundering Cycle
The process of ML, regardless of its degree of complexity, is accomplished in three stages, namely the placement stage, layering stage and integration stage.
-
Placement Stage
This involves the physical movement of the cash proceeds. For most criminal transactions, cash is the most common medium of exchange and criminals who accumulate large volumes of cash are the most vulnerable to detection and seizure. As a result, money launderers will attempt, through placement, to channel the funds into a bank.
-
Layering Stage
As a customer of the bank, you will need to liaise with your Relationship Manager or the bank staff that initiated your account opening.
LOAN POLICY
-
Purpose Of This Policy
The policies and procedures outlined in this document provide a framework within which the company is to operate its principal business of financing. This manual is meant to be a working document and a set of guidelines to be used by the Management Credit. These policies and procedures are flexible to enable the loan program to be responsive to market demands and are designed to be amended from time to time. The Board of Directors are authorised for approving and amending the Loan Policy.
-
Loan Products
The Company to advance under various categories of funding viz.,
Hire Purchase – It is an arrangement whereby a borrower agrees to a contract to acquire an asset by paying the price of the asset plus interest over a period of time in regular monthly installments.
Secured Loans – A secured loan is a loan in which the borrower pledges some asset as collateral for the loan, which then becomes a secured debt owed to the creditor who gives the loan. Types of Secured loan:
Hypothecation Loan - It means loan for which a charge in any movable property, whether tangible or intangible, present or future, created by a borrower without delivery of possession of the property
Mortgage is a loan in which immovable property is used as collateral.
Leasing - is a contract wherein the owner, called the Lessor, permits the user, called the Lessee, to use of an asset for a particular period which is shorter than the economic life of the asset without any transfer of ownership rights. The Lessor gives the right to the Lessee in return for regular lease payments for an agreed period of time.
Unsecured Loans – It means the loans not secured by any tangible or intangible asset.
This loan product list is intended to be only illustrative and not exhaustive. Depending on the opportunities available new products may be developed from time to time and added to these Loan Products with the approval of the Board of Directors.
The different variants of secured loans & advances, the company can decide on the ideal product mix/portfolio diversification looking into the pros and cons of each of the above category. However, the unsecured loans with higher degree to risk the company should take utmost care in proposal evaluation before disbursement and risk categorization and delinquencies management post disbursement. -
Portfolio Diversification Basics Of Lending
For a Finance Company, Money is the raw material as well as end product. Being NBFC, it raises funds from public/institutions/temples and Boards and lends the same to the borrowers as loan. As such the Company has to ensure that various borrowings will have to be properly serviced and the repayment will also have to be made promptly which necessitates prompt and punctual repayment by its borrowers.
To ensure prompt repayment by borrowers there should be a full pledged system for recovery of dues, even more is the selection of borrower to whom money is to be lent. If due care is taken in the selection of borrower, a good part of the Company’s efforts with regard to collections would have been taken care of. The need for a good credit appraisal system therefore gains more importance in this context.
Keeping this in mind the Company has drafted it Loan Policy covering Credit Appraisal and Documentation and Procedure for better business based on its experience and experimentation over the period of time. Each Company has its own risk appetite which determines the extent to which it can stretch its limits. The major question to address is whether one should avoid risk or manage risk. Once an organization is clear as to its goals, it becomes easier to draw the credit policy to enable its employees to administer the finance business. The credit policy of the Company comprises the following details
-- General guidelines outlining the various products on offer and the requirements to be met to consider the proposal for finance.
-- Mandatory documents to be collected under each category of customers depending upon the project for which the loan needs to be sanctioned.
-- Negative areas with respect to industry, profession, assets etc
--The circumstance under which deviations if any if permitted and if so the procedure to the followed under such instances
The activities involved are categorized into two major heads viz., pre-disbursement and post disbursement. Proper document forms major part of the pre-disbursement procedure and recovery plays a major role in post disbursement segment.
No matter how big or small the loan, no matter whether it is to an individual or to the largest multinational corporation, we follow certain principles of lending.This can be listed and remembered by the mnemonic IPARTS:
I NTEGRITY
P URPOSE
A MOUNT
R EPAYMENT
T ERM
S ECURITY -
Loan Policy Of The Company For Various Loan Products
TNTDFC will extend loan as per the object clause of the Memorandum of Association (MOA).
The lending rate interest will be decided by Asset Liability Committee on the regular basis (considering the market conditions or peer group).
The company mandate to raise funds through debt market and public deposits and primarily lends to State Transport Undertakings namely MTC, SETC, TNSTCs.
TNTDFC will lend to STUs by way of Term Loan to meet their Capital Expenditure on receiving Negative lien on unencumbered portion of the assets of the STUs as security.
GENERAL TERMS AND CONDITIONS
Amount of Loan - Decided by the Management depending on the fund flow
Nature of Assistance - Loan
Period - Maximum period of 5 years
Rate of Interest - Rates will be determined based on the deposit rates and weighted average capital. The rates will be the rate approved by the Board of Directors based on the recommendation of Asset Liability Management Committee
Repayment of Principal - The principal amount shall be repayable in monthly installments, payable on the last day of every month
Security - Depends upon the category of loan. It shall be mentioned in the loan agreement.
Pre- closure charges - The borrower may prepay on any date all or any part of the loan with the prior written permission from the company as per the terms and conditions decided by the Board. Loan On Deposits
A NBFC may grant a loan upto 70% of the amount of public deposit to depositors after the expiry of 3 months from the date of deposit at a rate as per the revision note*** above the interest rate payable on the deposits. Interest on loan will be adjusted out of the interest payable on Periodic Interest Payment Scheme Deposits (PIPS) and compounded basis on Money Multiplier Scheme Deposits (MMS) and recovered at the time of repayment of loan or on maturity of the said deposit. If the deposit is not claimed for refund / renewal, the loan, if any, on deposits with interest will be adjusted against the deposit on the date of maturity.
*** With effect from 01/01/2022, the loan interest will be charged @ 2% above the interest payable on deposits.
The quantum of loan against deposits has been reduced from 75% to 70% on the principle amount with effect from 01/12/2022.Risk Categorization And Delinquencies Management After Disbursement
Delinquencies can often indicate a need for additional business technical assistance. At the first sign of a late payment, the Management reviews the file and payment history and speaks with the borrower to determine the reason for the late payment.
The penal interest at the rate as decided by the Board will be levied for delayed repayment.
Depending on the days of delay in repayment of loan Risk categorization needs to be done. The Management and Asset Liability Committee may look into further action, with the approval of Board, if required, that may include:
1. Restructuring the loan
2. Implementing a strategy to liquidate the collateral.
3. Issuing a notice of default and the intention to repossess.
4. Draft an estimated time frame for recovery and a projected recovery amount.
PREVENTION OF SEXUAL HARASSMENT POLICY
-
Introduction
This policy is in accordance with the provisions of the Sexual Harassment of Women at Workplace (Prevention, Prohibition, and Redressal) Act, 2013. The purpose of this policy is to prevent sexual harassment against women in the workplace and also to protect them. Every company aims to provide a safe working environment for all people.
This policy is applicable to all the members of the company including employer and those who are employed on regular, temporary, on a daily wage basis, etc.
The policy also extends to those who are not employees of the company such as customers, clients, visitors, interns, contract workers, suppliers, etc.
This policy is restricted to the business locations of the company and any external location visited by the employees during the course of employment.
All the employees should have the personal responsibility to ensure that their behaviour is not in contravention with the policy.
Sexual Harassment
Any behaviour which may be physical, psychological, graphical, emotional, verbal, written, electronic, gestures which are offending, etc. is defined as inappropriate by the policy. Any act of the person either intentional or not, should not offend the dignity of the other person. If done so then serious disciplinary action is taken against the person who has performed such act.
Sexual harassment (direct or by implication) includes:
1. Any kind of unusual and unwelcome sexual requests or demand for sexual favors in return for employment, promotion, examination or evaluation of a person.
2. Stalking, displaying indecent posters, showing pornography, sending jokes, comments, messages which are inappropriate and sexual in nature, lurid stares, physical contact or molestation, inappropriate sounds, signs, questioning about personal private life or body, insults or taunts based on sex or any kind of communication either verbal or non-verbal which affects the performance of the individual.
3. Physical confinement against one will and likely to interrupt the privacy of the person.
4. Any act or conduct by a person who is in authority, which creates the environment at workplace hostile or intimidating to a person belonging to the other sex.
The complaints committee is responsible for receiving and investigating every complaint of sexual harassment, submitting findings and recommendation of the inquiry to the employer and coordinating with the employer before implementing any kind of appropriate action. The committee is also responsible to maintain confidentiality throughout the process.
It is the duty of the employer to provide a safe working environment and conduct awareness programs regarding the prevention of sexual harassment and provide necessary assistance and facilities to the committee in dealing with the complaints.
WHISTLE BLOWER POLICY
-
Preface
As per Section 177 of the Companies Act, 2013 and Rule 7 of the Companies (Meetings of Board and its Powers) Rules, 2014 requires every listed company, companies which accept deposits from the public and companies which have borrowed money from banks and public financial institutions in excess of fifty crore rupees to establish a vigil mechanism for the directors and employees to report genuine concerns or grievances about unethical behaviour, actual or suspected fraud or violation of the company's Code of Conduct or Ethics Policy. Such a vigil mechanism shall provide for adequate safeguards against victimization of directors and employees who avail of such mechanism and also make provisions for direct access to the Chairperson of Audit Committee in exceptional cases.
-
Policy
In compliance of the above requirements, Tamil Nadu Power Finance and Infrastructure Development Corporation Limited has established a Vigil (Whistle Blower) Mechanism and formulated a Policy in order to provide a framework for responsible and secure vigil mechanism/whistle blowing.
-
Policy Objectives
The Company is committed to adhere to the highest standards of ethical, moral and legal conduct of business operations. To maintain these standards, the Company encourages its employees who have concerns about suspected misconduct to come forward and express these concerns without fear of punishment or unfair treatment. A Vigil Mechanism/Whistle Blower Policy provides a channel to the employees and Directors to report to the management concerns about unethical behaviour, actual or suspected fraud.
-
Eligibility
All the directors and employees of the Company are eligible to make Protected Disclosures under the Policy in relation to matters concerning the Company.
-
Procedure
AAll Protected Disclosures should be reported in writing by the Whistle Blower as soon as possible, not later than 60 days after he becomes aware of the same. All Protected Disclosures should be addressed to the Chairman of the Audit Committee.
-
Decision
If an investigation leads the Chairman of the Audit Committee to conclude that an improper or unethical act has been committed, the Chairman of the Audit Committee shall recommend to the management of the Company to take such disciplinary or corrective action as he may deem fit. It is clarified that any disciplinary or corrective action initiated against the subject as a result of the findings of an investigation pursuant to this Policy shall adhere to the applicable personnel policy for staff conduct and disciplinary procedures.
CORPORATE SOCIAL RESPONSIBILITY POLICY
-
PREAMBLE
1. This policy has been prepared in pursuance of and in accordance with the requirements of Section 135 of the Companies Act, 2013 (hereinafter called as “the Act”) and the Companies (Corporate Social Responsibility Policy) Rules, 2014, notified by the Ministry of Corporate Affairs vide Notification dated 27th February, 2014 ( hereinafter called “CSR Rules”), as amended from time to time.
2. The main objective of the Policy is to lay down the general framework of action for TDFC to fulfil its Corporate Social Responsibility (hereinafter called “CSR”) and in particular to specify the activities and programs to be undertaken and also specify the modalities of execution and implementation and monitoring process of such programs.
3. This policy shall apply to all CSR initiatives and activities -
PROGRAMMES & PROJECTS
1. TDFC shall undertake projects in any one or more of the following focus areas: a. Promotion of education; b. Promoting health care including preventive health care
2. Within the focus areas mentioned in sub-clause 1 above, specific new projects may be approved by the Corporate Social Responsibility Committee ( hereinafter called ‘CSR Committee’), as deemed appropriate.
3. While undertaking CSR projects, preference shall be given to the area of operation of the Corporation in Tamil Nadu.
4. The CSR project shall not be any activity which is undertaken in pursuance of its normal course of business. The CSR projects or programs or activities that benefit only the employees of TDFC and their families shall not be considered as CSR activities in accordance with Section 135 of the Act. Any surplus arising out of the CSR projects or programs or activities shall not form part of the business profit of TDFC Ltd.
5. The CSR project shall comply with any other stipulation or restriction as provided under the CSR Rules or any clarification or circular issued by the Ministry of Corporate Affairs, from time to time -
MODALITY OF EXECUTION & IMPLEMENTATION
1. Each project may be executed in any of the following modes:
a. Either directly by TDFC Ltd. or
b. Through the Institute of Road Transport, Chennai.
2. While approving each specific project, the CSR Committee will prescribe the time period for implementation, mechanism for ensuring the end use of the funds and also appropriate reporting.
3. All proposals for a CSR project should be submitted to the Company Secretary who in turn will place it before the CSR Committee for necessary consideration and approval -
CSR BUDGET
1. The Annual CSR Budget shall be reviewed and recommended by the CSR Committee for each of the focus areas.
2. CSR projects or programs or activities undertaken in Tamil Nadu only shall amount to CSR Expenditure. The surplus, if any, arising out of any CSR project or program or activity shall not form part of the business profits of the Corporation. -
MONITORING & REPORTING
1.A report on progress of the CSR projects undertaken by the Corporation will be submitted to the CSR Committee with full details of cost incurred, date of completion and results achieved on a regular basis.
2. In order to ensure proper end use of the funds, officials may be deputed to personally inspect / verify the execution of the project / expenditure incurred.
3. A summarised report on implementation of the approved projects should be placed at least once in six months before the Committee.
4. CSR initiatives of the Corporation will be reported in the Annual Report of the Corporation in compliance with Section 135 of the Act, and rules made thereunder. -
AUTHORITY & AMENDMENTS
This Policy has been approved by the Board of Directors of the Company based on the recommendations of the CSR Committee. This policy may be amended from time to time by the Board, as it deems appropriate.
CORPORATE SOCIAL RESPONSIBILITY POLICY
-
CSR POLICY in tune with schedule VII of Companies Act, 2013
The CSR Policy of TNPFC is as follows:
1. Eradicating hunger, poverty and malnutrition, promoting healthcare including preventive health care and sanitation.
2. Promoting education, including special education and employment enhancing vocation skills especially among children, women, elderly, and the differently abled and livelihood enhancement projects.
3. Promoting gender equality, empowering women, setting up homes and hostels for women and orphans; setting up old age homes, day care centers and such other facilities for senior citizens and measures for reducing inequalities faced by socially and economically backward groups.
4. Ensuring environmental sustainability, ecological balance, protection of flora and fauna, animal welfare, agroforestry, conservation of natural resources and maintaining quality of soil, air and water.
5. Protection of national heritage, art and culture including restoration of buildings and sites of historical importance and works of art; setting up public libraries; promotion and development of traditional arts and handicrafts.
6. Measures for the benefit of armed forces veterans, war widows and their dependents.
7. Training to promote rural sports, nationally recognised sports, paralympic sports and Olympic sports.
8. Rural development projects.
9. Slum area development.
10. Promotion of Road Safety through CSR:
(i) (a) Promotions of Education, “Educating the Masses and Promotion of Road Safety awareness in all facets of road usage,
(b) Drivers’ training,
(c) Training to enforcement personnel,
(d) Safety traffic engineering and awareness through print, audio and visual media”.
(ii) Social Business Projects : “giving medical and Legal aid, treatment to road accident victims”.
11. Provisions for aids and appliances to the differently- able persons.
12. To make “Consumer Protection Services”
(i) Providing effective consumer grievance redressal mechanism.
(ii) Protecting consumer’s health and safety, sustainable consumption, consumer service, support and complaint resolution.
(iii) Consumer protection activities. (iv) Consumer Rights to be mandated. (v) all consumer protection programs and activities on the same lines as Rural Development, Education etc.
13. Disaster Relief.
14. Trauma care around highways in case of road accidents.
15. Rural development projects.
16. Enabling access to, or improving the delivery of, public health systems be considered under the head “preventive healthcare” or “measures for reducing inequalities faced by socially & economically backward groups”.
17. Slum re-development or EWS housing be covered under “measures for reducing inequalities faced by socially & economically backward groups”.
ASSET-LIABILITY MANAGEMENT POLICY
-
Introduction
Asset Liability Management Committee (ALCO) policy of the Corporation is aimed at managing the liquidity and Market risks. The present document seeks to integrate the overall concerns of managing Assets and Liabilities with specific accent on maximizing returns while controlling Liquidity and market risks.
The Policy is an exposition of the Corporation’s approach to funding, deployment and pricing of various resources and aims to create Systems and procedures to monitor, regulate and manage Liquidity and market risks. The management must necessarily operate within the Framework of the Corporation’s Vision and Mission along with Capital gearing, prudential Controls as per the regulatory compliance laid down from time to time by Reserve Bank of India. The Corporation’s ALM policy will pave the way for balance sheet positioning based on perception of Risk and Returns.
The Asset Liability Management Committee (ALCO) will oversee the implementation of ALM policy and review its functioning periodically and provide direction on interest rate for deposits and loans -
Asset Liability Coimmittee
Asset Liability Management Committee (ALCO) consist of
1. Joint Managing Director
2. Additional Secretary to Government of Taamilnadu, Finance (BPE) Department and
3. Independent Director -
Scope Of The Asset Liability Committee
1. To design, oversee and manage the Asset Liability Management System.
2. To decide the business and risk management strategy within the limit / parameters, if any, set by the Board.
3. To estimate and manage various components of assets and liabilities.
4. To manage credit risk, interest rate risk, liquidity risk, market risk and other operational risks.
5. Funding and capital planning.
6. Profit planning and growth projection.
7. Forecasting, analyzing and preparation of contingency plans and
8. Any other issues referred by the Board relating to ALMs, from time to time. -
The ALM policy covers the following areas of operations
1. Liquidity and Funding Risks
2. Market Risks
3. Credit Risk
4. Maintenance of liquid assets
5. Maturity Profiling
1. Liquidity and Funding Risks
Liquidity risk relates to potential inability to meet all payment obligations when they fail due or only being able to meet them at excessive costs. The objective of the liquidity risk management framework is to ensure that the company can fulfill its payment obligations at all times and can manage liquidity and funding risk within its risk appetite. The Asset liability Committee regularly monitors the liquidity position and the duration of assets/liabilities. The Company maintains liquidity ratio as per regulatory requirements by investing in government securities.
2. Market Risks
Market risk is the risk of loss arising from potential adverse changes in the value of the Company’s assets and liabilities from fluctuation in market variables like liquidity, interest rate and equity prices. Interest Rate Risk: The Company’s exposure to changes in interest rates relates to its investment in debt securities. All the debt securities of the Company is in local currency and on fixed rate basis and hence not subject to interest rate risk Currency Risk: The Company does not have any borrowings or investment in foreign currency and hence not subject to currency risk. Equity Risk: The Company has investments in listed companies, which are measured at Fair value through Profit and Loss. The valuation is dependent on market conditions
3. Credit Risk
Credit risk is the risk of financial loss to the Company if a customer fails to meet his contractual obligations, and arises principally from the Company’s loan receivables.The Company’s exposure is only to government department and retail loans against deposits. Loans against deposits are disbursed after retaining adequate margin and risk of default by the government department is also minimal. Hence, the Company is subject to limited risk. The Company applies the existing prudential norms and set out by Reserve Bank of India for NBFCs.
4. Maintenance of liquid assets
Non-banking Financial Companies holding public deposits are required to invest up to 15% of their public deposits in approved securities (called mandatory securities) in terms of liquid assets requirement of Section 45-IB of RBI Act, 1934.
5. Maturity Profiling
The Maturity Profile could be used for measuring the future cash flows of company in different time buckets that are to be maintained are as under.
1 day to 30/31 days (One month)
Over one month and up to 2 months
Over two months and up to 3 months
Over 3 months and up to 6 months
Over two months and up to 3 months
Over 6 months and up to I year
Over 1 year and up to 3 years
Over 3 years and up to 5 years
Over 5 years. -
Board of Directors Meetings and Review
The Board of Directors, in their board meetings, will oversee the implementation of the system and review its functioning and decision periodically.
INFORMATION TECHNOLOGY POLUCY
-
Introduction
The Information Technology Policy (IT Policy) provides an integrated set of protection measures that must be uniformly applied across Tamilnadu Transport Development Finance Corporation Ltd (TNTDFC LTD) to ensure a secured operating environment for its business operations.
Customer Information, organisational information, supporting IT systems, processes and people that are generating, storing and retrieving information are important assets of TNTDFC LTD. The availability, integrity and confidentiality of information are essential in building and maintaining our competitive edge, cash flow, profitability, and legal compliance.
This IT Policy addresses the information security requirements of:
1. Confidentiality: Protecting sensitive information from disclosure to unauthorised individuals or systems.
2. Integrity: Safeguarding the accuracy, completeness, and timeliness of information.
3. Availability: Ensuring that information and vital services are accessible to authorised users when required
Other principles and security requirements such as Authenticity, Non-repudiation, Identification, Authorisation, Accountability and audit ability is also addressed in this policy.
-
Scope
1. This policy applies to all staff, contractors, service providers, Interns/Trainees working in TNTDFC LTD. Third party service providers providing hosting services or wherein data is held outside TNTDFC LTD premises, shall also comply with this policy.
2. Scope of this IT Policy is the Information stored, communicated and processed within TNTDFC LTD and TNTDFC LTD’s data across outsourced service provider’s locations. -
Objectives
The objective of the IT Policy is to provide TNTDFC LTD, an approach to managing information risks and directives for the protection of information assets to all units, and those contracted to provide services -
Ownership
The Board of Directors of TNTDFC LTD is the owner of this policy and ultimately responsible for IT Policy -
Responsibility
To avoid conflict of interest formulation of policy and implementation / compliance to the policy to remain segregated. Therefore the Information Security Committee (ISC) will be the owner of the IT Policy and Implementation responsibility to rest with IT department of TNTDFC LTD.
The Information Security Officer (CISO) is responsible for articulating the IT Policy that TNTDFC uses to protect the information assets apart from coordinating the security related Issues within the organisation as well as relevant external agencies.
The CISO shall not be a member of IT department and shall be an Independent Director and member of Information Security Committee (ISC).
All the staffs and external parties as defined in policy are responsible to ensure the confidentiality, integrity and availability of TNTDFC’s information assets. -
Information Security Committee (ISC)
ISC to give recommendations regarding the Information Security risk and responsible for maintenance / review of the IS Policy and also for formulating/review of all sub policies derived from IS Policy. -
Policy Exceptions
Refer to Exception handling procedure. -
Periodic Review
The policy shall be reviewed every year or at the time of any major change in existing IT environment affecting policy and procedures, by CISO and placed to Board for approval.
This policy will remain in force until next review / revision. -
Policy Compliance Check
Compliance review of IS policy should be carried out by Internal/External auditor on a periodic basis. Inspection & Audit Division is responsible for monitoring compliance of IS Policy. The compliance report should be placed by IAD to the Audit Committee of Board. -
Information Security Governance
Information security governance consists of leadership, organisational structures and processes that protect information and mitigation of growing information security threats.
Critical outcomes of information security governance include:
1. Alignment of information security with business strategy to support organisational objectives
2. Management and mitigation of risks and reduction of potential impacts on information resources to an acceptable level
3. Management of performance of information security by measuring, monitoring and reporting information security governance metrics to ensure that organisational objectives are achieved
4. Optimisation of information security investments in support of organisational Objectives
It is important to consider the organisational necessity and benefits of information security governance. They include increased predictability and the reduction of uncertainty in business operations, a level of assurance that critical decisions are not based on faulty information, enabling efficient and effective risk management, protection from the increasing potential for legal liability, process improvement, reduced losses from security-related events and prevention of catastrophic consequences and improved reputation in the market and among customers -
Management Responsibility
1. Approve policies related to information security function 2. Ownership for implementation of board approved information security policy
3. Ownership for establishing necessary organisational processes for information security
4. Ownership for providing necessary resources for successful information security
5. Ownership for establishing a structure for implementation of an information security program (framework) -
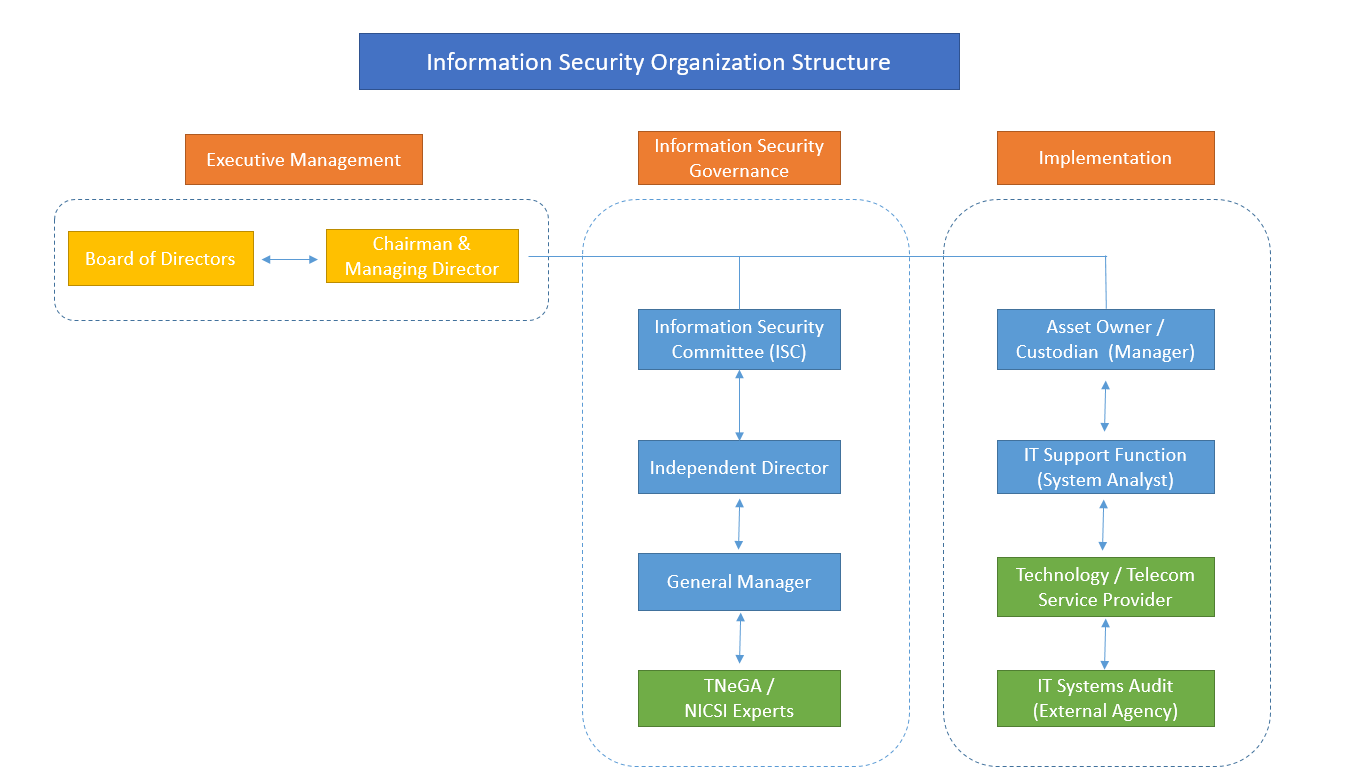
Organisation Structure
Information security organisation shall comprise of the following
1. Chairman & Managing Director
2. Board of Directors
3. Information Security Committee (ISC)
4. Information Asset Owner / Custodian
5. IT Support Function – System Analyst
6. IT System / Security Audit – External Certification Agency
-
The information Security Organisation is divided into 3 sections
1. Executive Management : Implementing effective security governance and defining the strategic security objectives of an organisation can be complex task. As with any other major initiative, it must have leadership and ongoing support from executive management to succeed.
2. Governance : Governance is the set of responsibilities and practices exercise by the board and executive management with the goal of providing strategic direction, ensuring that objectives are achieved, ascertaining that risks are managed appropriately and verifying that the enterprise resources are used responsibly.
3. Availability: Ensuring that information and vital services are accessible to authorised users when required -
Roles and Responsibilities
The roles and responsibilities of the Information Security Organisation members are as follows:
Board of Directors
1. Approving the Information Security Policy.
Information Security Committee (ISC)
1. The Independent Director shall be the chairman of the ISC. The ISC shall have the Joint Managing Director and representation from TNeGA or NICSI Experts
2. Members from Admin, HR, Legal, Finance and other departments should be called for the ISC meeting on need basis.
The ISC roles and responsibilities shall be as follows ,
1. Developing and facilitating the implementation of information security policies, and procedures to ensure that all identified risks are managed within a TNTDFC’s risk appetite.
2. Approving and monitoring major information security projects and the status of information security plans and budgets, establishing priorities, approving procedures.
3. Supporting the development and implementation of a TNTDFC-wide information security management program
4. Reviewing the position of security incidents and various information security assessments and monitoring activities across the TNTDFC
5. Reviewing the status of security awareness programs
6. Assessing new developments or issues relating to information security
7. Requirement for generating effective metrics for measuring performance of security control
8. Reporting to the Board of Directors on information security activities
9. Conducting regular ISC meetings (at least quarterly) and maintenance of MOM
-
Information Security Officer (CISO)
1. Establishing, implementing, monitoring, reviewing, maintaining and improving Information Security Management System (ISMS)
2. Reviewing the security policies/procedures and suggesting improvements
3. Coordinating the ISC meetings
4. Providing consultative inputs to the ISC on security requirements
5. Coordinating information Security initiatives in the organisation
6. Driving and monitoring the ISC directives in the organisation 7. Updating ISC about IS initiatives, issues and incidents
8. Facilitating and Conducting risk assessments of Information Assets used and recommend mitigation controls
9. Promote security awareness amongst staffs, customers and service providers -
Joint Managing Director
1. As a Head of Business Unit, Joint Managing Director is ultimately responsible for managing information risk in their respective business as part of their wider risk management responsibilities
2. Nominate Asset owner / Manager
3. Providing resources and support to the Asset Owners for information security implementation within TNTDFC LTD -
Information Asset Owner / Custodian – Manager
Information asset owners shall be allocated to each information asset and shall ensure that security processes associated with these assets are established. For data and IT systems, they are called as application owners. The asset owner or the application owner is usually the business owner. Each application should have an application owner (asset owner) who will typically be part of the concerned business function that uses the application.
Responsibilities would include, but not be limited to:
1. Assigning initial information classification and periodically reviewing the classification to ensure it still meets business needs under guidance of Information Security Committee (ISC)
2. Ensuring security controls are in place, as recommended by ISC
3. Reviewing and ensuring currency of the access rights associated with information assets they own
4. Determining access criteria and back-up requirements for the information assets / applications they own. -
IT Security Function – System Analyst
The IT Security is responsible for the execution of Information Risk policies, framework, guidelines and control processes.
The responsibilities of IT Security includes, but not limited to:
1. Enable Information Security controls
2. Define IT security procedures and guidelines in line with the IS Policies
3. Provide Security Architecture
4. Implement and monitor operational effectiveness of mandatory IT controls
5. Analysis of Security incidences, both internal and external and arriving at Lessons learned -
Technology Infrastructure Service Providers
1. Infrastructure services shall be provided by strategic outsourced partners with Service Level agreements. The service providers are custodians of IT assets on behalf of TNTDFC LTD and are responsible for the implementation and operation of the infrastructure as appropriate to meet the Confidentiality, Integrity and Availability ratings specified by TNTDFC LTD
2. Develop Standard Operating Procedures (SOP’s), Security Guidelines for the assets managed
3. Manage IT assets as per TNTDFC LTD approved policies and procedures. -
Application Developers
Application systems (including both business applications and generic supporting software, e.g. middle-ware, databases) may be developed and maintained by an internal IT function or by a third party. These parties are responsible for ensuring that systems are developed and maintained, incorporating user requirements and information security requirements that are in adherence to TNTDFC LTD Policies for Information Risk. They are also responsible, in conjunction with the provider of the underlying technology infrastructure, for ensuring that information risk is adequately managed in development and test environments and report to TNTDFC LTD IT Security -
User Manager
The user manager is the immediate manager or supervisor of the staff. User manager has the ultimate responsibility for all user IDs and information assets owned by TNTDFC staff. In the case of non-staff individuals such as contractors, consultants, etc., this manager is responsible for the activity and for the TNTDFC assets used by these individuals. He/she is usually the manager responsible for hiring the outside contractor -
End Users
1. End Users are responsible for the following with regard to information security.
2. Responsible and accountable for activities associated with an assigned account, as well as assigned equipment and removable media.
3. Protect secrecy of passwords and Business Information.
4. Report known or suspected security incidents -
Audit Team
Conduct information Security audits to check compliance against Policies and procedures. -
Policies, Procedures and Guidelines
At TNTDFC LTD considering the security requirements, Information Security policies have been framed based on a series of security principles. All the Information Security policies and their need have been addressed below: -
1. Asset Management Policy
Information assets shall be accounted for and have a nominated asset owner. Owners shall be identified and catalogued for all information assets and the responsibility for maintenance of appropriated controls shall be assigned. The implementation of specific controls may be delegated by the owner as appropriate but the owner remains accountable for the proper protection of the assets Ref: IT-Asset Management Guideline -
2. Information Risk management Procedure
Detailed risk assessments for Information risks (e.g. application risk assessment, Infra risk assessment) shall be undertaken in order to identify pertinent threats, the extent of vulnerability to those threats, the likelihood and the potential impact should a threat mature as a result of the vulnerability. This assessment shall determine acceptable, transferable and avoidable risk and the risk that shall be reduced by risk treatments (control mechanisms).
Ref: IT-Information Risk management Procedure -
3. Data Classification Policy
To ensure that Confidentiality, integrity and availability of information is maintained, a data classification scheme has been designed. The level of security to be provided to the information will depend directly on the classification of the data Ref: IT-Data Classification Guideline -
4. Acceptable IT Usage Policy
This Policy has been prepared and implemented to ensure that all the users and staff at TNTDFC LTD are aware of their responsibilities towards the IT Resources of TNTDFC LTD. This Policy details the end users aware of their responsibilities and the acceptable use of the IT Resources of TNTDFC LTD. Ref: IT-Acceptable IT Usage Guideline -
5. Access Control Policy
Data must have sufficient granularity to allow the appropriate authorised access. There is a delicate balance between protecting the data and permitting access to those who need to use the data for authorised purposes. This balance should be recognised. The Access Control Policy addresses this need. Ref: IT-Access Control Guideline -
6. E-mail Security Policy
TNTDFC LTD shall implement effective systems and procedures to ensure that e-mails are used as an efficient mode of business communication and implement control procedures so that the e-mail facility is not misused by the users. It also needs to be ensured that e-mail service and operations remain secure, efficient while communicating within intranet as well as through the internet. The Email Security Policy of TNTDFC LTD addresses this. Ref: IT-Email Security Guideline -
7. Internet & Intranet Security Policy
TNTDFC LTD should utilise Internet as an important resource for information and knowledge to carry on the business more efficiently. Users must also understand that any connection to the Internet offers an opportunity for unauthorised users to view or access corporate information. Towards this direction, TNTDFC LTD has developed systems & procedures to ensure that Internet is used only for business purposes in a secure manner, (without endangering the security of the TNTDFC LTD’s network) with a uniform code of conduct. Ref: IT-Internet & Intranet Guideline -
8. Password Security Policy
The purpose of this policy is to establish a standard for the creation of strong passwords, the protection of those passwords and the frequency of change all application software in TNTDFC LTD will have to comply with minimum password standards as specified in this document. Ref: IT-Password Security Guideline -
9. Information Security (IS) Incident Management Policy
Incident management is required and needs to be established to ensure a quick, effective, and orderly response to security incidents. Such a policy would vary in scope depending on the sensitivity and size of the information systems being managed. A companywide incident management policy has been established for all systems. Ref: IT-IS Incident Management Guideline -
10. IT-Change Management Policy
Changes to information technology facilities and systems should be controlled in order to ensure that changes made to a production component are applied in a secure and consistent manner Ref: IT-Change Management Guideline -
11. Application Security Policy
It may be required to develop and maintain software, applications and add-on modules from time to time. Proper procedures, access controls and security requirements need to be addressed in the entire process. The application security policy has been framed to address these needs. Ref: IT-Application Security Guideline -
12. Operating System Security Policy
TNTDFC LTD shall protect its operating system resources by providing security at a level that is appropriate for the nature of the data being processed. The operating system security policy has been framed for achieving this. TNTDFC LTD shall protect all business data, related application systems and operating systems software from unauthorised or illegal access. Access to the operating system must be restricted to those people who need the access to perform their duties. Ref: IT-Operating System Security Guideline -
13. Network Security Policy
Appropriate controls should be established to ensure security of data in private and public networks, and the protection of connected services from unauthorised access. TNTDFC LTD’s Network infrastructure needs to be protected from unauthorised access. A range of security controls is required in computer networks to protect these environments. Considering the above, the network security policy has been framed for TNTDFC LTD. Ref: IT-Network Security Guideline -
14. Anti-Virus Policy
Virus, Trojans, Worms, etc., are malicious programs called malware and can corrupt or destroy data or may spread confidential information to unauthorised recipients, resulting in loss of Confidentiality, Integrity, availability of the information. Malware detection and prevention measures as appropriate need to be implemented. The basis of protection against Malware should be founded on good security awareness and appropriate system access controls. The Anti-Virus policy has been framed on the above grounds. Ref: IT-Anti Virus Guideline -
15. Backup & Recovery Policy
In order to safeguard information and computing resources from various business and environmental threats, systems and procedures have been developed for backup of all business data, related application systems and operating systems software on a scheduled basis and in a standardised manner across TNTDFC LTD. The backup and recovery procedures must be automated wherever possible using the system features and be monitored regularly. The backup & recovery policy that has been framed for TNTDFC LTD considers these points. Ref: IT-Backup & Recovery Guideline -
16. Log and Audit Trail Policy
The log and audit trail policy addresses the framework for logging & auditing operating system events, application events, database events in the local area network and the network events. Ref: IT-Log and Audit Trail Guideline -
17. Mobile Computing Policy
The mobile computing policy applies to all TNTDFC LTD staffs and staff provided with a company laptop or portable electronic device. It is the staffs’ responsibility for the proper care and use of the laptop computer / PED (Portable Electronic Device), data and accompanying software while using the same. Ref: IT-Mobile Computing Guideline Ref: IT-Mobile Computing Guideline -
18. Version Control Policy
The version control policy of TNTDFC LTD addresses implementing, managing and controlling the changes in versions of application systems, and customised add-on modules, network and operating system software, interfaces and utilities. This Policy is aimed at ensuring uniformity in versions running across TNTDFC LTD and would involve maintaining up to date documentation for the entire version change process. Ref: IT-Version Control-Guideline -
19. Data Archival Policy
Proper data management will facilitate and improve the retrieval, evaluation, use and storage of critical and related information. The purpose of the data archival policy for TNTDFC LTD is to address the proper archival all its project related data as per the client requirement to support its high quality research service and also to ensure availability, integrity and confidentiality of the data. Ref: IT-Data Archival Guideline -
20. Encryption Policy
In the current environment of increasingly open and interconnected systems and networks, network and data information security are essential. This policy describes cryptography as a tool for satisfying a wide spectrum of the Information Security Management System (ISMS) needs and requirements. Ref: IT-Encryption Guideline -
21. Wireless Security Policy
Wireless Local Area Networks (LANs) form part of the TNTDFC LTD’s corporate network infrastructure. In order to protect the business needs of TNTDFC LTD, the wireless network must meet the same level of security employed by the rest of the infrastructure. This policy is to ensure that the deployment of wireless networking is controlled and managed in a centralised way to provide functionality and optimum levels of service whilst maintaining network security.
Ref: IT-Wireless Security Guideline -
22. Data Migration Policy
Sometimes, a need may arise to migrate data from one system / database to another. This typically occurs during replacement of existing application / database. This policy outlines the care to be taken during such migrations of data.
Ref: IT-Data Migration Guideline -
23. Security Awareness
All staff of TNTDFC LTD and, where relevant, contractors and third-party users shall receive appropriate awareness training and regular updates in organisational policies and procedures, as relevant for their job function -
24. Security monitoring
As per Cyber Security guidelines issued by RBI, a Security Operations Center shall be established for security monitoring of logs of critical IT Assets
Ref: Security monitoring procedure -
25. Hardware Acquisition & Maintenance
All staff of TNTDFC LTD and, where relevant, contractors and third-party users shall receive appropriate awareness training and regular updates in organisational policies and procedures, as relevant for their job function Ref: IT-Hardware Acquisition & Maintenance Guideline -
26. HR Security Guidelines
To ensure that staffs, contractors and third party users understand their responsibilities to reduce risk of theft, fraud or misuse of facilities, controls shall be implemented.
Ref: HR Security Guidelines -
27. Data Security Physical, Technical and Organisational Security Measures
Appropriate physical, technical and organisational security procedures that restrict access to and disclosure of personal data within TNTDFC are implemented. TNTDFC uses encryption, firewalls and other technology and security procedures to help protect the accuracy and security of sensitive personal information and prevent unauthorised access or improper use.
TNTDFC adapts RBI best practice guidelines for Physical, Technical and Organisational measures to ensure the security of personal data including the prevention of their alteration, loss, damage, unauthorised processing or access. -
28. Remote Access Policy
The purpose of this policy is to define standards for connecting to TNTDFC network from any host. These standards are designed to minimise the potential exposure to TNTDFC from damages which may result from unauthorised use of TNTDFC resources. Damages include the loss of sensitive or company confidential data, intellectual property, damage to public image, damage to critical TNTDFC internal systems, etc.
Ref: IT-Remote Access Policy -
29. Exception Handling Procedure
Information security policies and procedures constitute controls for protecting the Information assets. While every attempt should be made to comply with the policies and procedures there could be exceptions. The exception handling procedure should be followed for taking exceptions to the Information Security Policy. Ref: IT-Exception Handling Procedure -
30. Physical & Environmental security
To prevent unauthorised physical access, damage and interference to the organisations premises and information, critical or sensitive information processing facilities shall be housed in secure area, protected by secure parameters, with appropriate entry controls.
Ref: Physical Environment Guidelines -
31. Desktop Security Guidelines
The objective of desktop security guideline is to provide a secure computing environment where data is processed. All desktops on Local Area Network (LAN) shall be configured as per these guidelines. These guidelines are also applicable to Laptops provided by TNTDFC LTD to its staffs / contract staffs for its official use.
Ref: IT-Desktop Security Guidelines -
32. License Management Guidelines
TNTDFC uses operating systems, applications and database software that is under license agreement and limits the use of the software to specific machines. Copies of such software are limited to backups only. It is important to have a control on the use of software on the computers.
Ref: IT-License Management Guidelines -
33. Patch Management procedure
A Patch Management process needs to be in place to address technical system and software vulnerabilities quickly and effectively in order to reduce the likelihood of a serious TNTDFC’s Operations impact arising.
Ref: IT-Patch Management Procedure -
34. Asset Security Testing Procedure
With rapid use of Information Technology for processing financial data, and its use in day to business processes, evaluation of Information Security measures and implementation of an effective security monitoring controls has been identified as key requirements as per TNTDFC Information security policies.
Ref: IT-Asset Security Testing Procedure -
35. Effective Measurement
This document defines the metrics for collection and analysis of meaningful and quantifiable data to measure the effectiveness of the ISMS implementation. Metrics are to identify areas of improvements and formulate security strategies for continuously improving the security processes for the TNTDFC
Ref: IT-AIT-Effective measurement procedure -
36. Database Security Procedure
In accordance with the Information Security Policy, all databases owned by TNTDFC LTD must be adequately protected to ensure confidentiality, integrity, availability, and accountability of such systems. Databases normally provide a data storage mechanism as a back-end to an application that provides access to the data. In addition to electronic data storage, databases typically are associated with management systems which organise data into a collection of schemes, tables, queries, reports, views and other objects. Ref: IT-Database Security Procedure
-
37. Data Sanitisation Guidelines
Data Sanitisation is the process of protecting sensitive information in non-production databases from inappropriate visibility. After sanitisation, the database remains perfectly usable - the look and feel is preserved but the information content is secure. Data Sanitisation establishes relationship between technology and the expectation of privacy in the collection and sharing of personally identifiable information.
Ref: IT-Data Sanitisation Guidelines -
38. Key Management Procedure
Key management is the set of techniques and procedures supporting the establishment and maintenance of cryptographic key relationships between authorised parties within TNTDFC and its business partners, regulatory entities etc.
Ref: IT-Key Management Procedure -
39. Online Channels Security - Internet Banking & Mobile App
The implementation of appropriate authentication method and security controls should be based on assessment of the risks posed, and considering customer acceptance, ease of use, reliable performance, scalability to accommodate growth, and inter-operability with other systems. -
40. New Technology Adoption
1. Introduction of new technology and deployment of application & Infrastructure shall go through Risk assessment and sign off process before implementation in production.
2. Procedures and guidelines for new technologies shall be developed.
3. The risks associated with adoption of new & emerging technologies shall be assessed and approved. -
41. Cloud computing
Cloud computing requirements shall be assessed in detail for data security, privacy, legal requirements, sustainability of the provider, service levels, geographical location of data storage and processing, including trans-border data flows (if-any), business continuity requirements, log retention, data retention, audit trails, etc, during the risk assessment process. -
42. Social Media
Usage of Social Media within TNTDFC LTD’s network is restricted, unless approved specifically.
Staffs are personally responsible for the content they publish on-line, whether in a blog, social computing site or any other form of user- generated media.
Staffs are not authorised to publish or discuss the following on Social Media 1. TNTDFC LTD’s confidential or other proprietary information 2. To cite or reference Customers, partners or suppliers without their approval 3. To use TNTDFC LTD’s logos or trademarks unless approved to do so. -
43. Compliance
Compliance with Regulatory requirements.
1. Compliance to statutory, regulatory and contractual requirements such asInformation Technology Framework for the NBFC Sector, 2017, directives and recommendations given by Reserve bank of India shall be ensured
2. Compliance with terms/conditions and license requirements for the usage of copyrighted software or any other proprietary information/material shall be maintained
3. Cross border movement of data shall be in accordance with legal and regulatory requirements
4. Records shall be retained and managed based on legal and regulatory requirements
Compliance with Information Security policy and procedures
1. Information processing facilities shall be used as per information security policy and acceptable usage policy
2. While TNTDFC LTD respects the privacy of its staffs it reserves the right to audit and/or monitor the activities of its staffs and information stored, processed, transmitted or handled on any assets/devices/services used by staff
3. Exception to security policy and procedure shall be approved through the exception management process
4. Policy exceptions shall be reviewed at least annually and as deemed necessary based on security risks envisaged, emerging threats etc.
5. Violations or any attempted violations of security policies and procedures shall result in disciplinary actions
Information Systems Audit
1. Audits shall be conducted to ensure compliance with the information security policies, procedures and guidelines
2. The use of information systems audit tools shall be controlled and authorised to prevent any possible misuse of tools.